Tag: Linux
How to Install Jenkins on Ubuntu 20.04
How to Install Jenkins on CentOS 8
What is Jenkins?
Jenkins is an open-source software written in Java and Scala. This software allows users the ability to automate almost any task and, it saves significant time that can be better utilized addressing other issues. When automating tasks with Jenkins, users can optimize their workflow by quickly automating the jobs that servers cannot do themselves. In this tutorial, we will learn how to install Jenkins on CentOS 8. We will also explore what its purpose is and share several benefits that Jenkins offers. We will then configure it to run on our CentOS 8 server.
How to Install and Configure Bashtop
What is Bashtop?
Bashtop is a command-line based resource monitor written in bash, which depicts usage and statistics for the CPU processor(s), RAM, hard disks, network sources, and other running processes. It also contains a customizable menu and a fully responsive terminal user interface.
How to Set Up Plesk Backups in Cloud Object Storage
By default, Plesk typically stores backups on the server. This can, however, present a risk if the hard drive or RAID fails on the server. If this ever occurs, you can possibly lose both data and your backups. To avoid this situation, Liquid Web recommends storing additional backups in a remote storage location.
How to Install the Django Web Framework on Ubuntu 20.04
What is Django?

Django is a Python-based web framework that is used for developing complex, database-driven websites. It also operated under an open-source license indicating it is free to use. Django is ultra-fast and encourages security, and it is exceptionally adaptable, which is the cause of its immense popularity.
What is Containerization in DevOps?

Containers are the future of application development and hosting. They enable DevOps, developers, and system administrators to build, test, deploy, and maintain applications quickly, securely, and efficiently. Tools built around the containerization concept provide simple solutions for basic web applications. These advanced granular configuration options provide the control many enterprise applications may need.
Changing the SSH Port in WHM/cPanel in 3 Steps
While there are many ways to make sure your server is as secure as possible, there are some basic steps that we can take to increase security. Users with a Linux server can change their SSH port to something other than the SSH default port (22). The steps listed below outline how to change SSH port numbers and enable the change.
How to Install and Configure Rancher K3s
What is Rancher K3s?

K3s is an official Cloud Native Computing Foundation sandbox project that brings a lightweight, fully compliant Kubernetes distribution designed for lower resource production models like remote locations or on an IoT device. When used in conjunction with Rancher, K3s can easily be managed from within the Rancher orchestration platform.
What is Infrastructure as Code? (IaC)
Introduction: What is IaC?
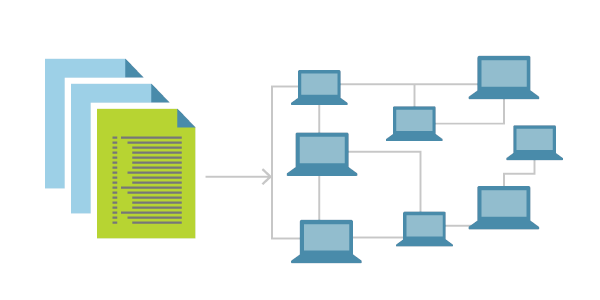
Today we will become acquainted with a concept known as Infrastructure as Code. The idea of Infrastructure as Code is becoming more and more popular today. IaC is a method used to manage and provision a data center via defined machine-readable files instead of physical hardware configuration or other interactive configuration tools. This article will share what it is used for, why it is important, and why businesses strive to utilize this platform to achieve a desired set of results. It is essential to understand that we will consider both the theoretical and practical parts of IaC.
How to Implement Zero Trust Security in 5 Steps
What is Zero Trust Security?
Zero Trust security is the concept, methodology, and threat model that assumes no user, system, or service operating within a secured internal environment should be automatically trusted. It put forward that every interaction must be verified when trying to connect to a system before being granted access. This concept uses micro-segmentation, and granular edge controls based on user rights, application access levels, service usage, and relation to the location to determine whether to trust a user, machine, or application seeking to access a specific part of an organization.
Our Sales and Support teams are available 24 hours by phone or e-mail to assist.

